
There have been an alarming number of devastating cyberattacks around the world in 2022, including in the United Kingdom and Ireland.
One example is the ransomware attack on KP Snacks, the manufacturer of Hula Hoops, Nik Naks, Tyrells, and many other snacks. An attack by a Russian cybercrime group caused supply chain problems for approximately two months, resulting in millions of dollars in damages.
Although this attack received national media coverage, there were many other more harmful attacks on smaller businesses.
In 2022, it is more obvious than ever that all businesses are at risk of cyberattacks and must take steps to reduce their cyber risk. The majority of businesses know this, but some lack basic security controls, such as multifactor authentication.
A multifactor authentication system is essential for all businesses, which we will explain in this blog.
Ten years ago we needed VPN (Virtual Private Network) connect to our email, access our files in the office and look up clients in our customer database. Today, the majority of this is accessible from any location, any device and anytime. This era of easy access exposes your business applications to the whole world. A password isn’t going to cut it anymore.


The number one reason why businesses should implement MFA is that it will strengthen their security posture. In 2022, the most common form of cyberattack is phishing, with 83% of all cyberattacks in the UK being phishing attacks.
Whilst multifactor authentication will not stop phishing attacks, it does significantly reduce the chance of a phishing attack being successful in compromising a user’s account.
For example, many phishing attacks include a malicious link that will take the user to a false sign-in page. Even if an employee was to click on the link and enter their username and password if multifactor authentication is enabled, the bad actor will have the username and password, but they will not have the second form of authentication. Whilst it is possible for a bad actor to social engineer their way into acquiring the second form of authentication, it is significantly less prevalent, and can be mitigated in several ways.
If your business needs to be industry standards, multifactor authentication is a necessity. For example, the PCI-DSS (Payment Card Industry Data Security Standard) requires businesses to have MFA enabled for remote access to the cardholder data environment.
Although for PCI-DSS, the only requirement is for a single environment, in order for businesses to achieve their Cyber Essentials certification they must implement MFA on administration accounts, and any accounts that are accessible via the internet.
Most insurance companies will require companies to implement multifactor authentication on all accounts in order to qualify for cyber insurance.
Whilst it may seem counterintuitive that adding another step to logging in will improve the user experience, multifactor authentication can be implemented alongside single sign-on to both improve security and the user experience.
Single sign-on, or SSO, is a technology that allows employees to authenticate credentials once in order to access all the systems, services and solutions required for their role. This includes all Microsoft applications, as well as thousands of other SaaS applications.
This improves the user experience and increases productivity as it means that employees spend less time entering credentials, and they only need to remember one password and have one method of multifactor authentication. It also strengthens the organisation’s security posture as there is no need for employees to reuse the same password across different accounts.
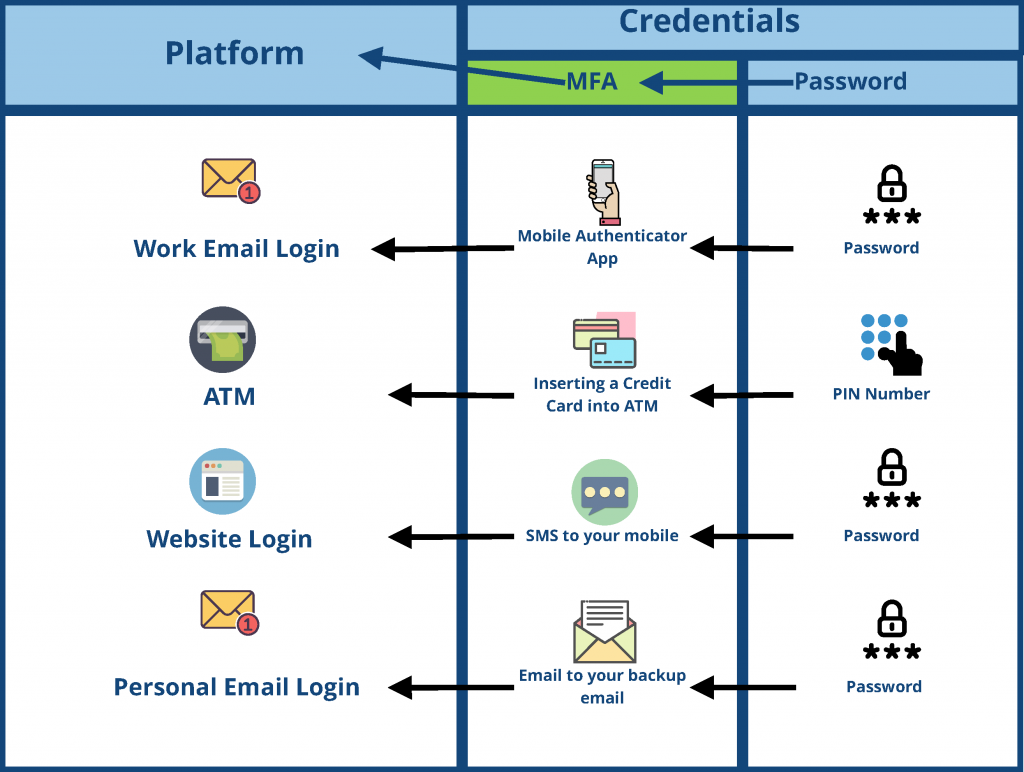
A username and password you have are called One-Factor Authentication, something you know. Two-Way Authentication is something you have physically, like a phone or a hardware token.
The physical device is unique to yourself and is recognised by the system. It will confirm its presence by either sending push message asking you confirm that this is you. So you log into your online accountancy system on your desktop computer, your mobile requests you to confirm this is you logging in.
As this typically relies on two-way communication, it doesn’t always lend itself to everyday situations. So another way is a one-time password or code. Based on the time of the day, your device will generate what seems like a random set of numbers. The requesting application the other end knows what these numbers will be.
Let’s both agree on a secret number, say 5 and never mentioned it again.
When we want to talk to one another, we’ll ask for a code to confirm identity. The code will be current time in minutes plus our secret number. So if the time were 17 minutes past the hour, our reply would be 22.
Secret Number + Time = One time code
The other party would do the same sum and expect the answer 22. The verification process has happened without actually communicating the secret number 5.
Then imagine this process scaled up using large sets of numbers and complex mathematics.
Hopefully, you already use some form Two-Way Authentication with online banking? An app on your smartphone or little calculator device that generates a code everytime you need to check your balance.
Most cloud service providers give you the option to switch on Two-Factor Authentication. Other on-premise and traditional applications can use broker service that does the authentication part.
It’s now becoming mainstream for phones to have a built-in fingerprint reader. So an application accepts your password, something you know. Which in turn trusts your phone, something you have. Finally, your phone verifies you’re the rightful owner via recognition of your fingerprint, something you are.
Before getting started, make sure to have the Microsoft Authenticator app installed on your mobile device.
If you’d rather watch a video on setting MFA for 365, watch the below 2 minute video from Microsoft.
Multifactor authentication is essential for businesses of all sizes, within all industries. However, many businesses do not have the required expertise to implement MFA correctly, especially if they want to use SSO.
We can help you implement multifactor authentication, as well as SSO and even passwordless authentication. It is also important to note that MFA is not the only security control required to protect your business from cyberattacks. We can also protect your entire IT ecosystem with a comprehensive security solution, tailored to your business needs. To find out more, contact us today.